Enhancing IoT Cybersecurity through Multi-Technique Data Anonymization: A Differential Privacy Framework Using Public IoT Datasets
DOI:
https://doi.org/10.62019/tdjz6f05Keywords:
IoT, Cybersecurity, Multi-Technique, Differential PrivacyAbstract
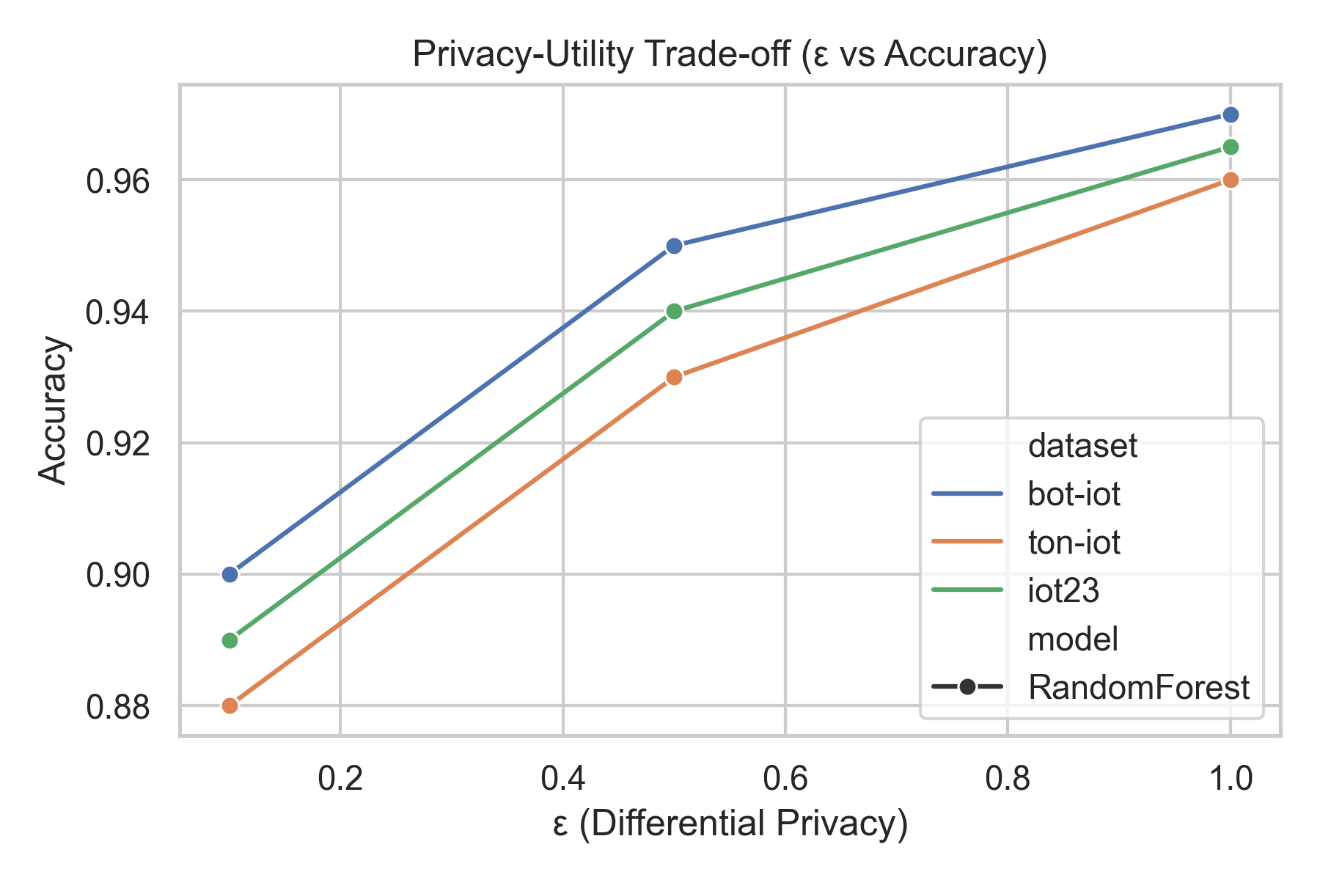
The proliferation of Internet of Things (IoT) deployments in critical domains such as smart homes, healthcare, and industrial control has significantly expanded the attack surface of modern networks. While the security research community increasingly relies on public IoT network traces to design intrusion detection systems (IDS), the release and sharing of such datasets raise serious privacy concerns for end-users, operators, and infrastructure providers. Building on recent work on scalable anonymization and privacy-preserving big data analytics, this paper proposes a unified data anonymization framework that combines ɛ-differential privacy (DP) with classical k-anonymity and l-diversity to protect sensitive information while preserving the utility of IoT cybersecurity datasets. We instantiate the framework conceptually on three widely used public benchmarks Bot-IoT, TON_IoT, and IoT-23 and design a reproducible pipeline to study the privacy-utility trade-off under different privacy budgets. Informed by recent advances in IoT security, big data analytics, and differential privacy for multimedia and sensing, we focus on moderate privacy budgets (e.g., ɛ in the range 0.5-1.0) that are known to offer a favorable balance between privacy protection and model utility. The paper contributes (i) a single-column description of the anonymization and evaluation pipeline, (ii) a multi-technique anonymization framework tailored to public IoT datasets, and (iii) design guidelines for dataset publishers and security practitioners grounded in existing literature on scalable anonymization.
Downloads
Published
Issue
Section
License

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.